Introduction
Destructive cyberattacks—using malware, wipers, or modified ransomware—aim to destroy data, erase evidence, or render systems inoperable. While the risk of reprisal limits their frequency, geopolitical instability can trigger a surge. This guide provides actionable steps to proactively prepare and harden your environment against such attacks, leveraging scalable methods that also thwart reconnaissance, privilege escalation, lateral movement, and persistence. Effective monitoring requires deep understanding of your environment and established baselines; the custom detection opportunities here supplement existing tools.
What You Need
- Endpoint and network security tools (e.g., EDR, NDR) with signature and heuristic capabilities
- Out-of-band communication platform completely decoupled from corporate identity systems
- Pre-validated incident command structure and contact lists for key stakeholders and third-party support
- Documented operational contingency and recovery plans including manual procedures for vital business functions
- Baseline understanding of normal network and endpoint behavior in your environment
- Executive buy-in for crisis preparation as part of security governance
- Regular tabletop exercise cadence and testing schedule
Step-by-Step Hardening Process
Step 1: Establish an Out-of-Band Incident Command and Communication Platform
Select and validate a communication system that operates independently from your primary identity plane. This ensures key stakeholders and third-party support teams can coordinate securely even if corporate email, chat, or collaboration tools are compromised. Key actions:
- Choose a platform not federated with your main directory (e.g., alternate Signal group, dedicated satellite phone, or separate VoIP system).
- Test the platform quarterly with all incident responders and critical business owners.
- Document the activation procedure and distribute physically (hard copy) to avoid digital lockdown.
Step 2: Define Operational Contingency and Recovery Plans
Identify your most critical business functions and document manual workarounds. Develop recovery runbooks that cover complete restoration from clean backups, including network rebuild, system reimaging, and data restoration. Key actions:
- Inventory all essential services and dependencies.
- Create step-by-step manual procedures for each vital function (e.g., manual order processing if ERP is down).
- Store recovery plans in an out-of-band location and in hard copy.
- Test full recovery at least annually, and partial failover exercises quarterly.
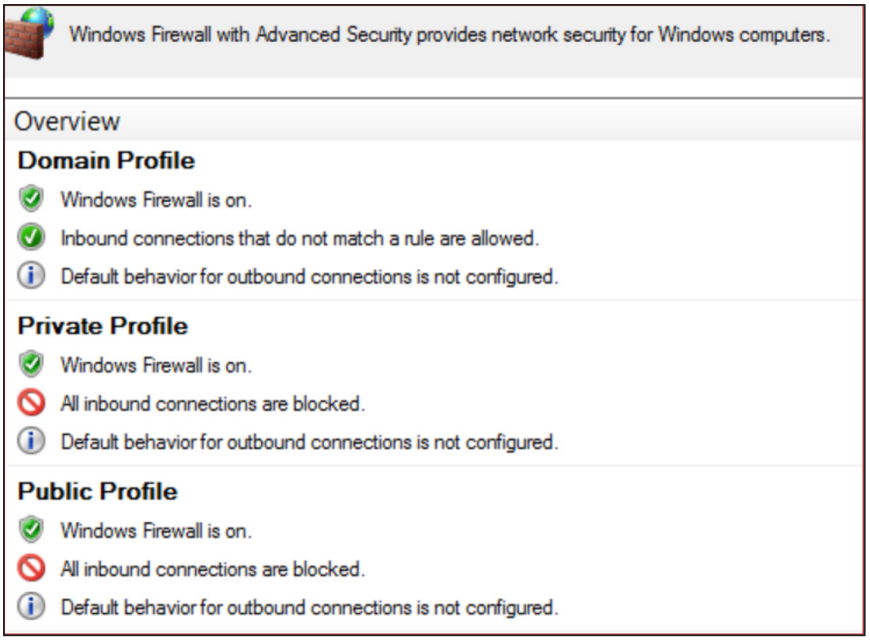
Step 3: Deploy and Tune Endpoint and Network Security Tools
Leverage EDR and NDR tools with signature-based and heuristic detection. Tune them to your environment’s baseline to reduce false positives. Key actions:
- Install agents on all endpoints and servers.
- Enable behavioral detection rules that trigger on mass file deletion, shadow copy removal, or unusual process launches.
- Configure network security tools to alert on outbound connections associated with known C2 infrastructure or bulk data transfers.
Step 4: Develop Custom Detection Opportunities Correlated to Threat Actor Behavior
Create monitoring rules that detect divergence from normal patterns. Focus on behaviors observed in past destructive attacks: mass data wiping, privilege escalation attempts, and lateral movement via remote execution tools. Key actions:

- Build detections for abnormal use of
vssadmin,wmic, orcscript. - Monitor for unauthorized installation of drivers or kernel modules.
- Alert on bulk SMB/CIFS operations across many hosts in a short window.
- Correlate events with threat intelligence feeds for known destructive actor TTPs.
Step 5: Monitor for Abuse or Misuse of Endpoint/MDM Platforms
Attackers may leverage legitimate mobile device management (MDM) or endpoint management tools to push destructive configurations or wipe devices. Key actions:
- Review MDM console logs for unauthorized profile changes, remote wipes, or mass device unenrollment.
- Restrict administrative access to MDM platforms using privileged identity management.
- Set up alerts for any action that could remotely disable or wipe endpoints (e.g., iOS Device Wipe, Android Factory Reset commands).
Step 6: Integrate Crisis Preparation into Security Governance
Make resilience a living part of your organization by embedding crisis orchestration into governance structures. Key actions:
- Assign a crisis management team with clear roles and out-of-band contact information.
- Conduct bi‑annual tabletop exercises simulating a destructive attack scenario.
- Include crisis communication planning (internal and external) in your security program.
- Review and update plans after each exercise or real incident.
Tips for Success
- Know your baseline: Effective detection depends on deep understanding of what is normal in your environment. Invest in continuous baseline monitoring and review.
- Test recovery, not just detection: Practice restoring from clean backups in a sandbox environment; many organizations fail at the recovery step.
- Keep backups offline: Ensure immutable or air‑gapped backups exist to prevent deletion by destructive malware.
- Document everything: Manual procedures, communication trees, and system architecture should be available even if digital copies are destroyed.
- Engage executive sponsorship: Destructive attack readiness requires budget and organizational will; present risk scenarios to leadership clearly.
- Stay current: Update detection rules and tools quarterly based on evolving threat intelligence and post‑incident lessons learned.